-
Add login succeeded event to post registration hook (#3739) (b685fa5)
-
Add missing env vars to set up guide (#3855) (da90502):
Closes https://github.com/ory/kratos/issues/3828
-
Add missing indexes and remove unused index (6d7372e)
-
Add missing indexes and remove unused index (#3756) (c905f02)
-
Add sms mfa via parameter to spec (#3766) (b291c95)
-
Allow updating just the verified_at timestamp of addresses (#3880) (696cc1b)
-
Always issue session last (#3876) (e942507):
In post persist hooks, the session issuance hook always needs
to come last. This fixes the getHooks function to ensure this.
-
Audit issues (#3797) (7017490)
-
Change return urls in quickstarts (#3928) (9730e09)
-
Close res body (#3870) (cc39f8d)
-
CVEs in dependencies (#3902) (e5d3b0a)
-
Db index and duplicate credentials error (#3896) (9f34a21):
- fix: don't return password cred type if empty
- fix: better index for config.user_handle on identity_credentials
-
Do not require method to be passkey in settings schema (#3862) (660f330)
-
Don't require connection_uri in SMTP (#3861) (800f8f1)
-
Don't treat passkeys as AAL2 (#3853) (8eee972)
-
Drop index if exists (#3846) (ad0619d)
-
Drop trigram index on identifiers (#3827) (8f8fd90)
-
Enum type of session expandables (#3891) (63d785e)
-
Enum type of session expandables (#3895) (c435727)
-
Execute verification & verification_ui properly in login flows (#3847) (5aad1c1)
-
Ignore decrypt errors in WithDeclassifiedCredentials (#3731) (8f5192f)
-
Improve SDK discriminators (#3844) (c08b3ad)
-
Include all creds in duplicate credential err (#3881) (e06c241)
-
Linkedin issuer override (#3875) (11d221a)
-
Make sure emails can still be sent with SMS enabled (#3795) (7c68c5a)
-
Missing indices and foreign keys (#3800) (0b32ce1)
-
oidc: Grace period for continuity container on oidc callbacks (#3915) (1a9a096)
-
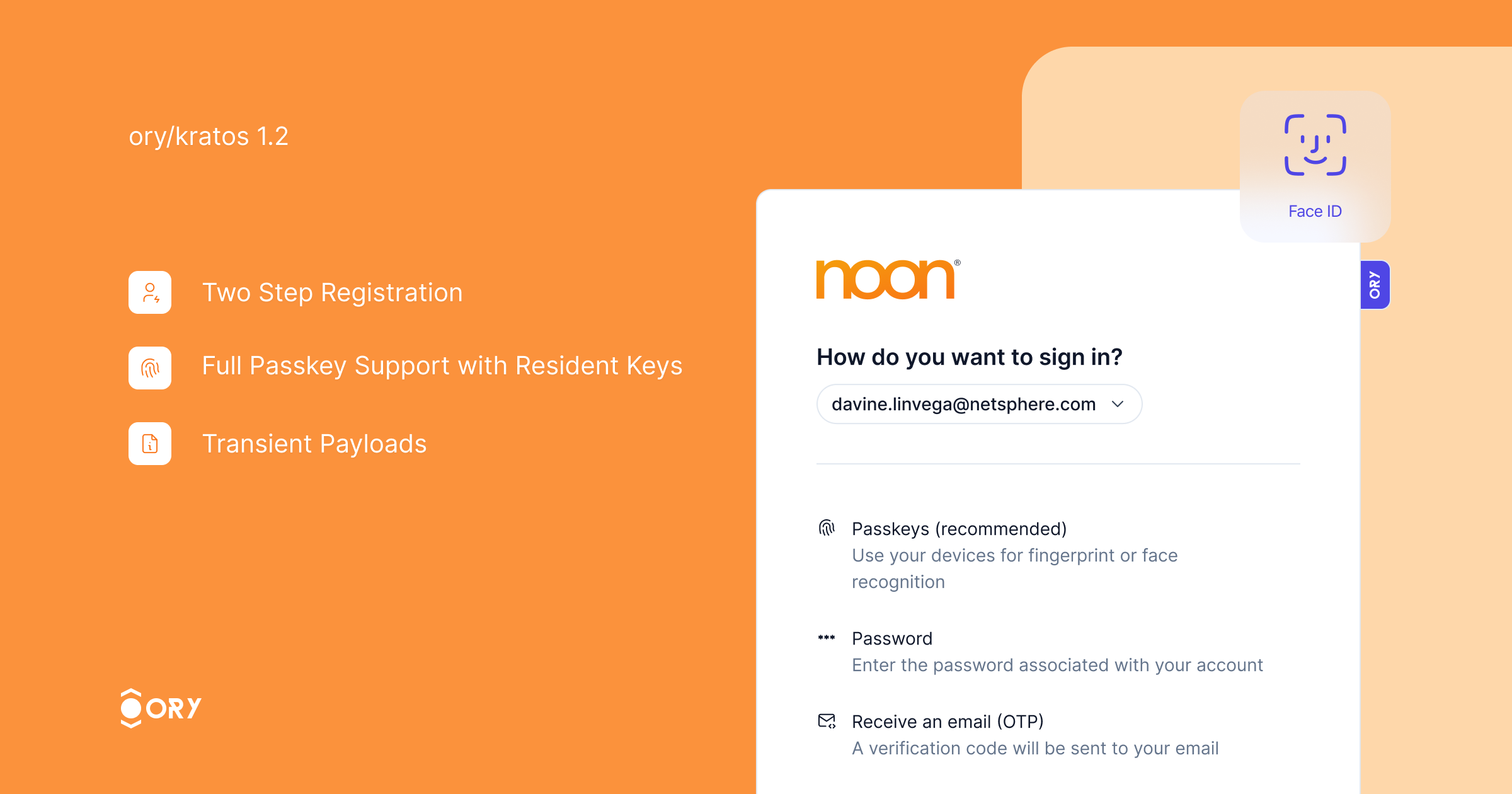
Passing transient payloads (#3838) (d01b670)
-
Prevent SMTP URL leak on unparsable URL (#3770) (c5f39f4)
-
Respect return_to in OIDC API flow error case (#3893) (e8f1bcb):
- fix: respect return_to in OIDC API flow error case
This fix ensures that we redirect the user to the return_to URL
when an error occurs during the OIDC login for native flows.
Native flows are initialized through the API, and the browser
URL is retrieved from a 422 response after a POST to submit the
login flow. Successful OIDC flows already returned the code to
the return_to URL. Now, unsuccessful flows return the flow with
the current flow ID (which might have changed), so that the caller
can retrieve the full flow and act accordingly.
- fix: ignore trivvy CVE report
Bump in distroless is still open
-
sdk: Expand identity in session extension (#3843) (04f0231), closes #3842
-
sdk: Improve discriminators for node and Go (#3821) (9ddf7cc)
-
Show error page on identity mismatch (#3790) (e6db689)
-
Test assertions on declassifying OIDC tokens (#3773) (7f8a7f1)
-
Tolerate more "truthy" values when creating new flows (#3841) (49d93c0), closes #3839:
Use strconv.ParseBool to accept multiple "truthy" values for the
refresh and return_session_token_exchange_code query parameters when
creating a new login flow.
For some SDKs (e.g.: Python), these stringification of booleans is not
user-controlled and these endpoints could not be used fully due to the
backend ignoring any value other than true (all lowercase).
-
Tweaks to UpsertSessions (#3878) (da51dcd)
-
Use correct post-verification identity state in post-hooks (#3863) (6e63d06)
-
Webhook transient payload in OIDC login flows (#3857) (2cdfc70):
- fix: transient payload with OIDC login