-
Add additional messages (735fc5b)
-
Add browser return_to continue_with action (7b636d8)
-
Add if method to sdk (612e3bf)
-
Add redirect to continue_with for SPA flows (99c945c):
This patch adds the new continue_with action redirect_browser_to, which contains the redirect URL the app should redirect to. It is only supported for SPA (not server-side browser apps, not native apps) flows at this point in time.
-
Add social providers to credential discovery as well (5f4a2bf)
-
Add support for Salesforce as identity provider (#4003) (3bf1ca9)
-
Add tests for two step login (#3959) (8225e40)
-
Allow deletion of an individual OIDC credential (#3968) (a43cef2):
This extends the existing DELETE /admin/identities/{id}/credentials/{type} API to accept an ?identifier=foobar query parameter for {type}==oidc like such:
DELETE /admin/identities/{id}/credentials/oidc?identifier=github%3A012345
This will delete the GitHub OIDC credential with the identifier github:012345 (012345 is the subject as returned by GitHub).
To find out which OIDC credentials exist, call GET /admin/identities/{id}?include_credential=oidc beforehand.
This will allow you to delete individual OIDC credentials for users even if they have several set up.
-
Allow partially failing batch inserts (#4083) (4ba7033):
When batch-inserting multiple identities, conflicts or validation errors of a subset of identities in the batch still allow the rest of the identities to be inserted. The returned JSON contains the error details that lead to the failure.
-
Better detection if credentials exist on identifier first login (#3963) (42ade94)
-
Change method=profile:back to screen=previous (#4119) (2cd8483)
-
Clarify session extend behavior (#3962) (af5ea35)
-
Client-side PKCE take 3 (#4078) (f7c1024):
This change introduces a new configuration for OIDC providers: pkce with values auto (default), never, force.
When auto is specified or the field is omitted, Kratos will perform autodiscovery and perform PKCE when the server advertises support for it. This requires the issuer_url to be set for the provider.
never completely disables PKCE support. This is only theoretically useful: when a provider advertises PKCE support but doesn't actually implement it.
force always sends a PKCE challenge in the initial redirect URL, regardless of what the provider advertises. This setting is useful when the provider offers PKCE but doesn't advertise it in his ./well-known/openid-configuration.
Important: When setting pkce: force, you must whitelist a different return URL for your OAuth2 client in the provider's configuration. Instead of /self-service/methods/oidc/callback/, you must use /self-service/methods/oidc/callback (note missing last path segment). This is to enable the use of the same OAuth client ID+secret when configuring several Kratos OIDC providers, without having to whitelist individual redirect_uris for each Kratos provider config.
-
chore: regenerate SDK, bump DB versions, cleanup tool install
-
chore: get final organization ID from provider config during registration and login
-
chore: fixup OIDC function signatures and improve tests
-
Emit events in identity persister (#4107) (20156f6)
-
Enable new-style OIDC state generation (#4121) (eb97243)
-
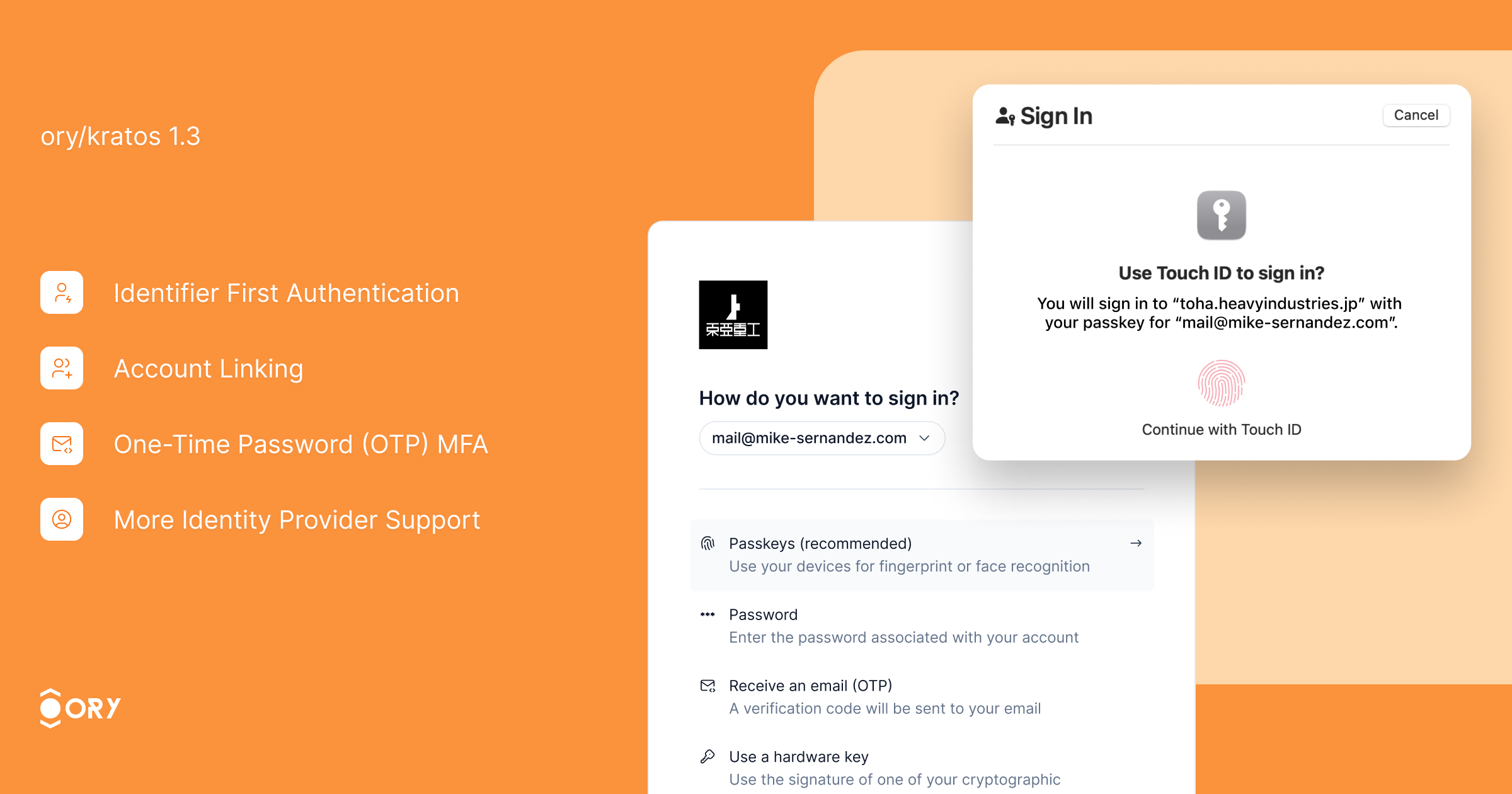
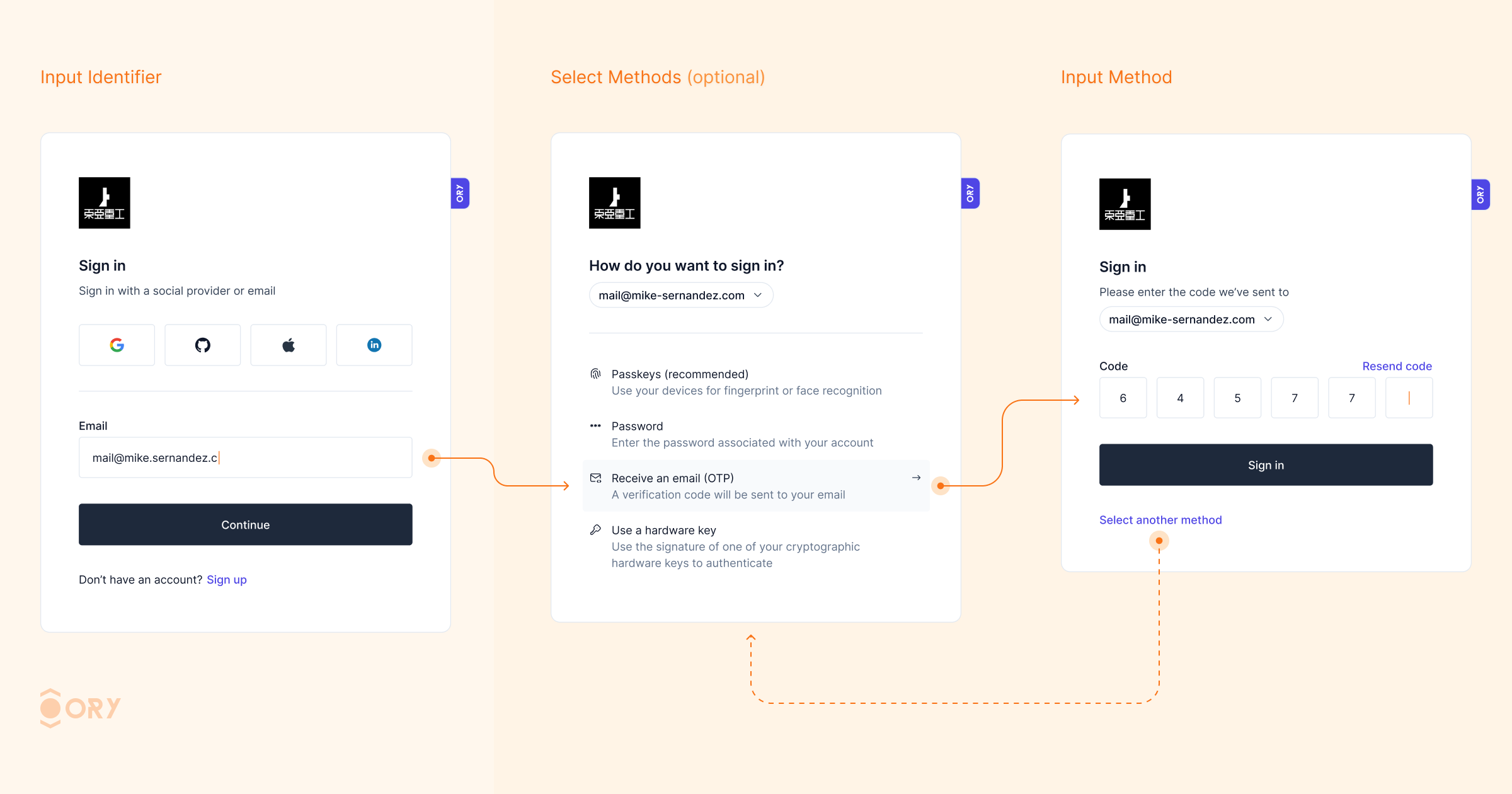
Identifier first auth (1bdc19a)
-
Identifier first login for all first factor login methods (638b274)
-
Improve session extend performance (#3948) (4e3fad4):
This patch improves the performance for extending session lifespans. Lifespan extension is tricky as it is often part of the middleware of Ory Kratos consumers. As such, it is prone to transaction contention when we read and write to the same session row at the same time (and potentially multiple times).
To address this, we:
- Introduce a locking mechanism on the row to reduce transaction contention;
- Add a new feature flag that toggles returning 204 no content instead of 200 + session.
Be aware that all reads on the session table will have to wait for the transaction to commit before they return a value. This may cause long(er) response times on /session/whoami for sessions that are being extended at the same time.
-
Password migration hook (#3978) (c9d5573):
This adds a password migration hook to easily migrate passwords for which we do not have the hash.
For each user that needs to be migrated to Ory Network, a new identity is created with a credential of type password with a config of {"use_password_migration_hook": true} .
When a user logs in, the credential identifier and password will be sent to the password_migration web hook if all of these are true:
The user’s identity’s password credential is {"use_password_migration_hook": true}
The password_migration hook is configured
After calling the password_migration hook, the HTTP status code will be inspected:
On 200, we parse the response as JSON and look for {"status": "password_match"}. The password credential config will be replaced with the hash of the actual password.
On any other status code, we assume that the password is not valid.
-
sdk: Add missing profile discriminator to update registration (0150795)
-
sdk: Avoid eval with javascript triggers (dd6e53d):
Using OnLoadTrigger and OnClickTrigger one can now map the trigger to the corresponding JavaScript function.
For example, trigger {"on_click_trigger":"oryWebAuthnRegistration"} should be translated to window.oryWebAuthnRegistration():
if (attrs.onClickTrigger) {
window[attrs.onClickTrigger]()
}
-
Separate 2fa refresh from 1st factor refresh (#3961) (89355d8)
-
Set maxlength for totp input (51042d9)